Trust & Authentication for Next Generation (TA4NGI) is a project consisting of a proof of concept for next generation security technology. It enables authentication and transport protocol encryption by implementing TLS-KDH as authentication mechanism into the Open-Source Software Satosa.
NGI Pointer Project
Key people: Peter Gietz
Affiliation: DAASI International
Trust and authentication, what is broken?
First, let´s define what we are talking about:
Trust means that we can be sure that one piece of information reaches the person it is addressed to, and no one else is receiving the information.
Authentication means that I prove that it is me who is interacting with the system and the system recognizes me.
These concepts are at the very heart of internet security. Currently, security tools are consolidated, some of them based on technologies from decades ago but still valid: although the computing capabilities increase, (in a way) we only need to lengthen our passwords and we will still be protected.
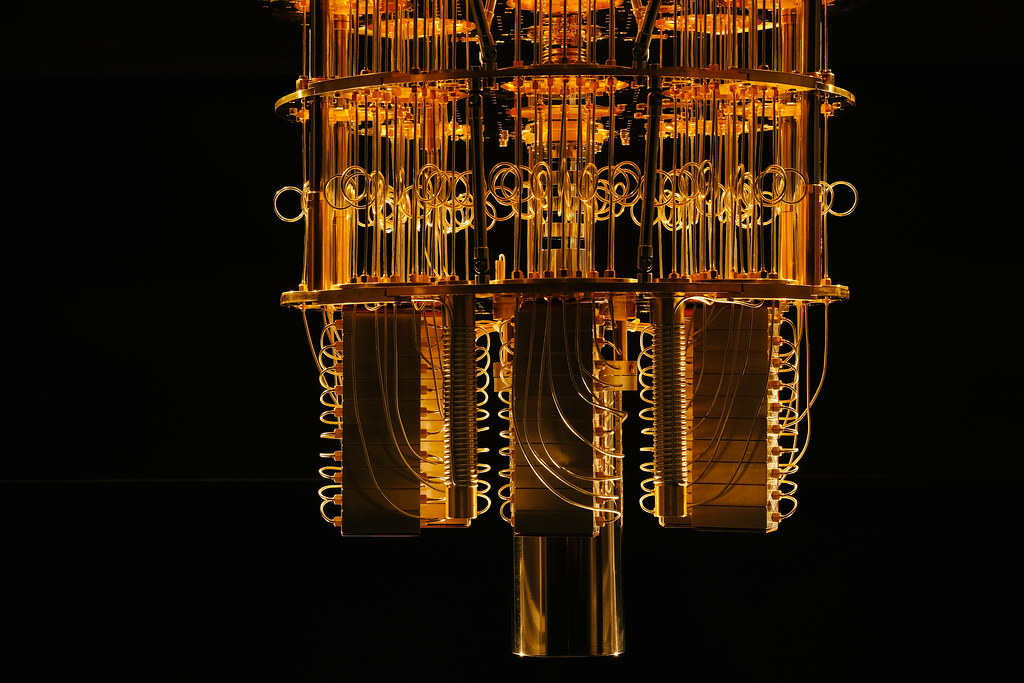
This is true for current computing systems, but with quantum computing (QC) on the verge of a revolution, current encryption systems like RSA (a public-key cryptosystem widely used) will no longer be valid so we need new tools to make internet communications safe again.
<<Quantum computing demands new tools for enhancing security, lengthen our pasword will not be enough anymore.>>
Developing security tools for the Quantum Computing era
Nowadays, quantum computing (QC) is already working in labs around the world. In the future it will boost its performance not by a factor of ten, but of hundreds or thousands.
In the future, the brightest guys in QC will develop security solutions based on QC itself. But in the meantime, we need a more practical approach, like using current technologies and their combinations to generate new tools to improve security.
This is precisely what the people from DAASI International are focused on within TA4NGI project: new developments from the combination of TLS-KDH (Transport Layer Security – Kerberos Diffie Hellman). The key is to take the strength of each component and put them together to create a new tool that enhances security as well as usability.
Let’s break it down:
– TLS is mostly used for encryption, securing communications;
– Kerberos (K) is mostly used for authentication, signing once, and using several services under that initial signature; and
– DH is a mechanism to agree mutually on a key that cannot be cracked.
<< TA4NGI’s approach: to develop new (open source) security tools by the combination of existing technologies>>
When encryption is not working properly, the problem is on the implementation side
Heartbleed, was a security bug in the OpenSSL cryptography library, one of the most used implementations of the Transport Layer Security (TLS) protocol, and one of the open-source software´s biggest bugs (failures?) to its date. It showed us the importance of preventing any mistakes, otherwise the best algorithms will not secure our data.
According to DAASI International´s CEO Peter Gietz, the key is to focus on a strong peer-review process, to avoid new Heartbleeds in the future, leaning in the strengths of open-source: experienced people, and strong processes, assuming that no featured code will be merged in real code before another person reviews the code.
<<The key of open-source is to focus on the methodology of process (peer)reviewing.>>
Open-source software, yay or ney?
At TA4NGI, DAASI International´s team is not completely reinventing the wheel. TLS-KDH uses established protocols and that also means it can be used for well-established software.
We saw with Heartbleed that you can have bugs in professional software, but with open-source software you have the chance to reach a broad team of professionals to peer review the changes that eventually will lead to more secure software.
<<Security by obscurity is not the answer: a strong argument for open-source.>>
Similar bugs like Heartbleed were found in Apple software. It is much more difficult to find bugs in closed software. It happens only via exploits, but they occur.
In open-source you have the chance to embark bright people to look at the code and find bugs before they are exploited.
The role of NGI Pointer in TA4NGI project
Projects like TA4NGI need to prove trustworthy to the community. You need enough people saying that the implementation is secure, and then developers will take it up.
At this moment there is a paradigm shift where the key is self-sovereign, identity, empowerment.
Whilst the USA is focused on the commercialization of the information, and China seeks to know all
about their citizens to maintain the status quo. Europe has the chance to create its third way: human
rights in the centre of the debate, neither commercialization nor population control.

Europe could try to win the security race by leaning on human rights. regarding quantum computing, Europe is falling behind, with China leading the race (burning money on the
topic).
<<Putting the human rights in the centre of the Internet debate is the third way Europe must lead.>>
Long process
Developing new security tools is a long endeavour. We will reach the day where QC will be unthinkable faster than current computing, and so it is never too early to start thinking of the issues or threats linked to it. In this interval we find ourselves, one of the most promising solutions is the one proposed by DAASI International´s team in TA4NGI project funded by NGI Pointer.
We will keep an eye on its development!
If you want to read more about NGI you can find other blogposts under the NGI category. For example, take a peek at the Gossip Protocol – Scuttlebutt here.





